Integracja z listami bezpieczeństwa
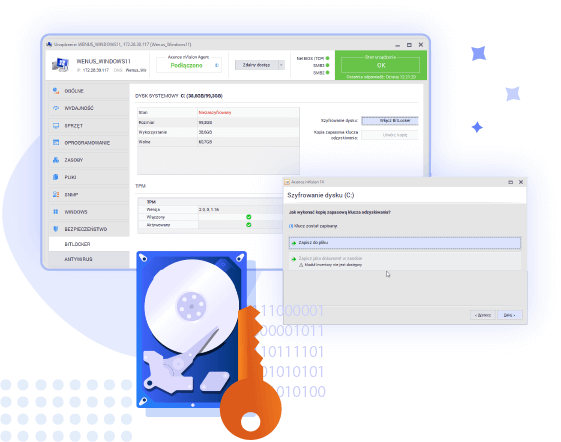
Zdalne szyfrowanie dysków
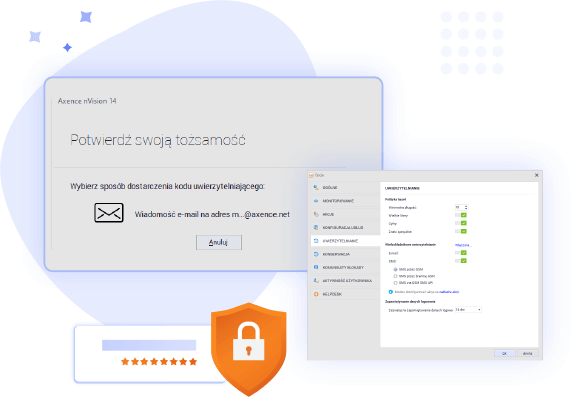
Bezpieczne logowanie
Monitorowanie i zarządzanie maszynami wirtualnymi

W nowym Axence nVision® otrzymasz jeszcze więcej narzędzi dla pełni bezpieczeństwa Twoich danych, sieci i użytkowników.
W wersji 14.5 dostarczamy szereg funkcjonalności, które umocnią Twoją architekturę bezpieczeństwa: mechanizmy logowania i uwierzytelnienia, integrację z listami bezpieczeństwa w tym z listą ostrzeżeń CERT.pl, zdalne szyfrowanie z BitLocker i wiele więcej.
Bezpieczniej niż kiedykolwiek z nVision 14.5!
Najważniejsze nowości
Blokuj niebezpieczne strony dzięki integracji z listami bezpieczeństwa - w tym z listą ostrzeżeń CERT.pl
Internet pełen jest niebezpiecznych serwisów, a użytkownicy mogą łatwo paść ofiarą podejrzanych linków. Na szczęście istnieją serwisy, które rejestrują niebezpieczne adresy. Od teraz te listy mogą być wdrażane do polityki blokad Axence nVision®. Wprowadzamy mechanizm, który umożliwia łatwe i globalne propagowanie centralnej listy blokowanych stron, tworzenie list blokowania stron, współdzielonych między grupami i użytkownikami oraz wydajną obsługę list dla dziesiątek tysięcy blokowanych adresów.
W Axence nVision® dostępna będzie domyślna lista ostrzeżeń serwisu CERT.pl (do ręcznej aktywacji) oraz możliwość pobierania dowolnych list ze wskazanych adresów.
Zwiększ bezpieczeństwo logowania dzięki uwierzytelnieniu wieloskładnikowemu - kontrola dostępu na najwyższym poziomie!
Bezpieczeństwo dostępu do konsoli Axence nVision® ma najwyższy priorytet, dlatego wprowadzamy uwierzytelnianie wieloskładnikowe (MFA), które pozwoli podnieść poziom ochrony organizacji. Użytkownicy będą musieli potwierdzić swoją tożsamość przy użyciu co najmniej dwóch różnych metod, takich jak kod autoryzacyjny wysłany przez e-mail i/lub SMS. Wprowadzamy również wymogi dla haseł zgodne z aktualnymi standardami, w tym możliwość ustalenia długości hasła, obecności wielkich liter, cyfr i znaków specjalnych, oraz regułę automatycznego wymuszania zmiany hasła.
Wykorzystaj MFA i silniejsze metody autoryzacji, aby zapewnić wzmożoną ochronę dostępu i uchronić infrastrukturę przed nieuprawnionymi próbami logowania.
Zabezpiecz dane na dyskach z BitLockerem - proaktywna ochrona informacji
Zdalne zarządzanie IT i wsparcie pracowników poza biurem to kluczowe możliwości Axence nVision®. Dzięki zintegrowanej funkcji zdalnego szyfrowania dysków z BitLockerem, zapewniasz swoim danym najwyższy poziom ochrony. Nowa funkcjonalność pozwala na zdalne zlecanie szyfrowania zarówno dysku systemowego, jak i pozostałych dysków podłączonych do komputera, zabezpieczając je przed nieautoryzowanym dostępem - nawet w przypadku kradzieży lub utraty sprzętu. Konsola Axence nVision® umożliwia administratorom zarządzanie i bezpieczne przechowywanie zapisanych kopii klucza odzyskiwania, chroniąc cenne dane przed atakami hakerów.
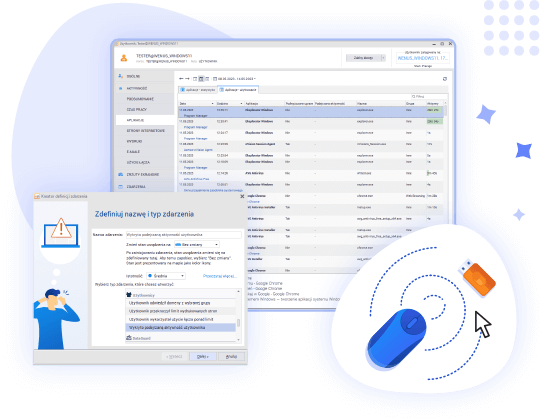
Wykrywaj podejrzaną aktywność użytkowników i jigglery
W nowej wersji Axence nVision® wprowadzamy mechanizm wykrywania podejrzanej aktywności użytkowników, takiej jak użycie jigglerów - urządzeń generujących symulowany ruch myszką. Nasze rozwiązanie analizuje podejrzane zachowanie użytkownika, zamiast identyfikować podłączone urządzenia fizyczne, co pozwala na wykrycie popularnych jigglerów oraz przyszłych zagrożeń opartych na tej samej zasadzie.
Axence nVision® pozwala na monitorowanie i rozliczanie aktywności użytkowników, umożliwiając definiowanie alarmów na wykrycie takiej aktywności oraz wyświetlanie jej w raportach. Dodatkowo, w momencie wykrycia podejrzanej aktywności, dostępna jest opcja automatycznych zrzutów ekranu użytkownika.
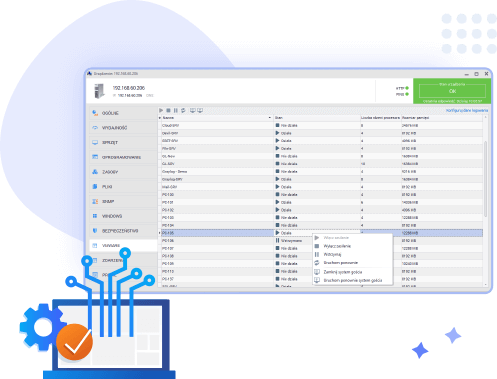
Monitoruj i zarządzaj maszynami wirtualnymi VMware - optymalizacja kontroli nad infrastrukturą IT
Wprowadzamy rozszerzenie naszego bezpłatnego modułu Network, które umożliwia monitorowanie i zarządzanie maszynami wirtualnymi VMware. Teraz nVision prezentuje listę maszyn wirtualnych wraz z ich aktualnym stanem (działa, nie działa, wstrzymano), co pozwala na lepszą kontrolę i zarządzanie tymi zasobami. Dodatkowo, oferujemy możliwość wysyłania poleceń włączenia zasilana, wstrzymania oraz wyłączenia zasilania dla każdej maszyny wirtualnej, co pozwala na jeszcze większą elastyczność w monitorowaniu i zarządzaniu infrastrukturą IT.
Changelog
Zobacz pełną listę zmian i nowych funkcjonalności
Uwierzytelnianie wieloskładnikowe (Multifactor Authentication/MFA):
- •Wymaganie MFA przy logowaniu do desktopowej konsoli nVision
- •Wysyłanie kodu autoryzacyjnego (6 cyfr) za pomocą e-mail i/lub SMS. Obsługa obu numerów telefonów w profilu użytkownika (stacjonarny, komórkowy).
- •Określenie limitu czasowego dla zapamiętania loginu użytkownika.
- •Dostęp awaryjny do konsoli - możliwość pominięcia uwierzytelniania MFA, jeśli konsola nVision i serwer nVision są zainstalowane lokalnie na tej samej maszynie.
Wymogi dla haseł użytkowników w nVision:
- •Ustalenie długości hasła, obecności wielkich liter, cyfr i znaków specjalnych.
- •Automatyczne wymuszanie zmiany hasła, gdy ktoś zaloguje się do desktopowej konsoli z hasłem niespełniającym wymogów.
Wykrywanie jigglerów i innej podejrzanej aktywności:
- •Wykrywanie, gdy użytkownik przez minimum 15 minut wyłącznie rusza myszką lub ma wciśnięty ten sam klawisz.
- •Uniwersalny mechanizm analizy zachowania użytkownika, wykrywający popularne na rynku jigglery oraz przyszłe, działające na podobnej zasadzie.
- •Zdefiniowanie alarmu na wykrycie podejrzanej aktywności i wyświetlenie jej w raportach.
- •Włączenie zrzutów ekranu dla użytkownika, które automatycznie rozpoczną się w momencie wykrycia podejrzanej aktywności.
Integracja z zewnętrznymi listami blokowania stron, w szczególności z listą CERT.PL
- •Mechanizm globalnego propagowania centralnej listy blokowanych stron w obrębie wszystkich Agentów.
- •Tworzenie list blokowania stron współdzielonych między atlasem, grupami i użytkownikami
- •Zwiększenie wydajności list blokowania stron
- •Automatyczne pobieranie dynamicznych list blokowania stron w formie pliku TXT z dowolnego wskazanego adresu
- •Domyślna lista dynamiczna na start z serwisu CERT.pl (wymaga ręcznej aktywacji)
Zacznij korzystać z nowej wersji
Posiadasz ważną umowę serwisową (SA)
Pobierz za darmoNie masz aktualnej umowy serwisowej?
Zamów wycenę